Timesys Device Security Solutions
Leverage Timesys’ engineering and security expertise, and dedicate your resources to helping your client develop their next-generation product.
Timesys Device Security Solutions
Leverage Timesys’ engineering and security expertise, and dedicate your resources to helping your client develop their next-generation product.
It’s no secret that securing and maintaining Linux OS is complex and time consuming, and it’s required for the entire product lifecycle — often 10 years. This includes but is not limited to:
- Vulnerability monitoring and management: filtering, analyzing, triaging, and remediating CVEs
- Kernel updates to keep up with long-term support branch and kernel patches and minor versions
- Toolchain updates for glibc bug fixes, security patches, and more
- BSP updates to libraries and packages anywhere from 1 to 4 times per year
- Testing and re-testing of Linux BSP/platform and functional testing of drivers
What if you could provide your client with a cost-effective solution to offload the routine Linux OS/BSP maintenance for the entire product lifecycle of their device?
Long-term Security Updates and Maintenance for Linux OS/BSPs
Timesys Linux OS/BSP Maintenance simplifies meeting industry compliance requirements:
Connected Devices: UL 2900-1 — ANSI/CAN/UL Standard for Software Cybersecurity for Network-Connectable Products
Medical: FDA Premarket and Postmarket Security Guidance, IEC 62304, NEMA Requirements for Manufacturer Disclosure Statement for Medical Device Security, and NEMA MDS2 Requirements

IIoT & Industrial: IEC 62443, ISA99, IEC 29147 and 30111 for Vulnerability Handling and Disclosure, NERC CIP Standards, NIST Special Publication 800-82, UK CPNI Internet of Things and Industrial Control Systems guidelines

IoT: ETSI EN 303 645 — Cyber Security for Consumer Internet of Things, NIST 8259 Foundational Cybersecurity Activities for IoT Device Manufacturers, 8259A IoT Device Cybersecurity Capability Core Baseline

Automotive: ISO/SAE 21434, European WP.29 Compliance, NHTSA Draft 2020 recommendations for Software and Firmware Security

Create an accurate Software Bill of Materials (SBOM)

Monitor and manage vulnerabilities for 3rd party software

Keep software updated with security fixes

Provide documentation of lifecycle security processes
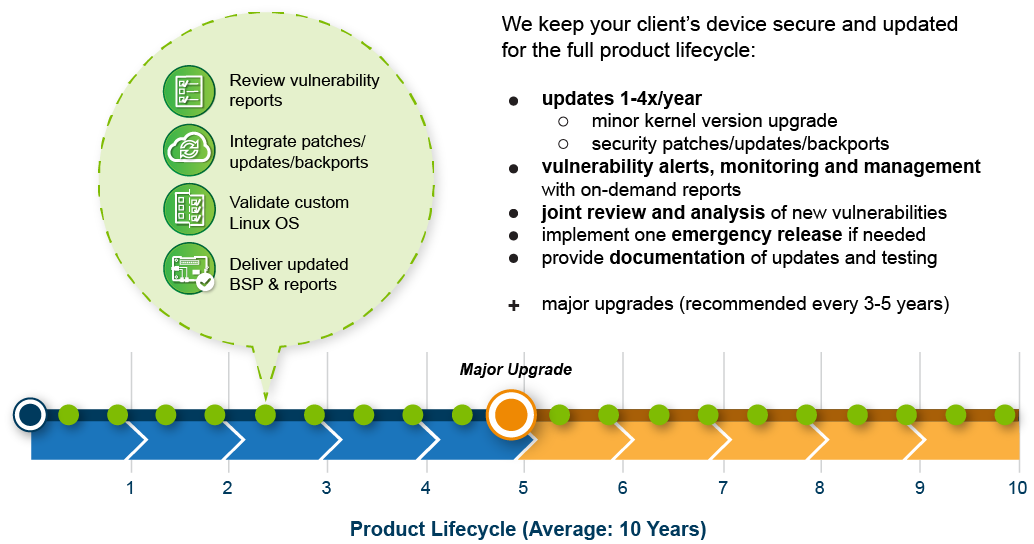
Timesys Linux OS/BSP Maintenance
How It Works
Set Up
Baseline
We set up a baseline that includes:
- Adding your client’s custom board into the Timesys Embedded Board Farm
- Adding your client’s BSP code into a private Git repo that only you, your client and Timesys can access
- Running a driver test
Review
Reports
We provide monthly vulnerability reports, and on a quarterly basis we jointly review them to determine what updates and patches you want us to apply.

Integrate Patches / Updates / Backports
We integrate security patches / package updates and backports for your BSP as per the quarterly review.

Validate Custom
Linux OS
After integrating patches / updates, we validate the BSP by comparing the driver tests against the baseline.
Deliver Updated BSP
& Reports
We deliver updated BSP and validation reports for comparison with the previous report.
 Translate
Translate