Vigiles Prime Tutorial: Part 1 – Getting Started with the Core Features
A Quick Walk-through and Process Tutorial
Introduction
This page will walk you through the core features of Vigiles so you can immediately start monitoring vulnerabilities affecting your embedded Linux product. By the end of this walk-through, you’ll be able to get your software bill of materials (SBOM) into Vigiles, run a scan, and see the highly accurate CVE list for your product.
Note: Vigiles can also be used as a general CVE monitoring tool for RTOS-based systems. To learn more, contact us.
Here’s the Recommended Vigiles Workflow

Getting a Software Bill of Material (SBOM)/Manifest into your account, Scanning for CVEs, and Reading and Interpreting the Scans

As you can see above, the process we’ll cover in this tutorial starts with your build and then capturing your build information in a software bill of materials (SBOM)/manifest. Note: This does not scan your source code or binaries. From there, Vigiles will scan your SBOM/manifest and generate a report that you can analyze to determine which vulnerabilities you want to address.
Now let’s get you started …
Logging Into Vigiles
Log in to the Timesys LinuxLink portal to access your Vigiles dashboard here: https://linuxlink.timesys.com/login/. Then click on the “Vigiles Dashboard” button.
Getting A Software Bill of Materials (SBOM)/Manifest Into Your Account

Sample Manifest
If it’s your first log-in, the sample manifest that we’ve provided for you in your Vigiles Private Workspace will automatically trigger a scan and take you to the CVE dashboard where you can view the scan results.
Sample Manifest
You can proceed with the sample manifest for now, or you can go back and upload your own manifest. There are three routes you can use to get your own manifest into Vigiles. They are:
Route 1 — Via Build Integration
If you are using Yocto, Buildroot, or Timesys Factory, try to use build integration. This method will capture your kernel and U-Boot configuration, a better mapping of your packages names to CVE naming, package versions, and any patches that have been applied. The integration will also upload your manifest to your account into the appropriate product and automatically kick off the scan.
From Yocto
From Buildroot
From within Timesys Desktop Factory
Route 2 — Uploading a CSV
You can generate a CSV of your software packages, versions, and patch information as well as your kernel and U-Boot configuration to upload into Vigiles.
From a Software Bill of Materials (SBOM) in .csv format
Route 3 — Using the Create Manifest Wizard
You can also put together a manifest through the Vigiles manifest builder. Going this route is tedious, but it’s an option if you can’t utilize the build integration or CSV generation route.
With the Create Manifest Wizard
Scanning Your SBOM/Manifest

Vigiles automatically triggers a scan of the SBOM/manifest specific to your product configuration against a Timesys-curated vulnerabilities database.
Reading/Interpreting the CVE Scans

The CVE dashboard page is made up of three sections. Here’s how to interpret the results of your scan:
1. Summary Section
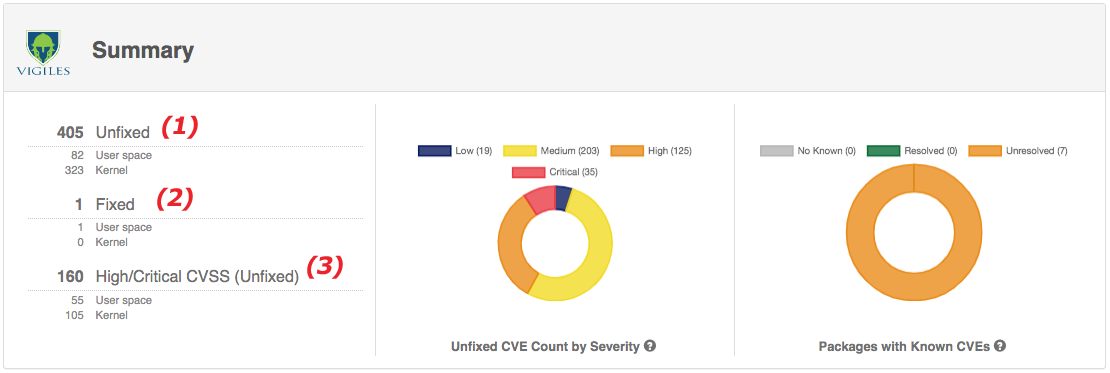
The summary will give you an overview of the vulnerabilities that apply to your SBOM.
- Unfixed: shows how many CVEs are unfixed in your current build. A mitigation may or may not exist for these vulnerabilities.
- Fixed: shows how many CVEs have been patched based on your manifest information. This information is only provided for manifests generated via build system and advanced CSV manifests with applied patches included.
- High/Critical CVSS (Unfixed): shows how many CVEs that have a CVSS Score of 7 or greater on a scale of 0 to 10.
2. Packages Section
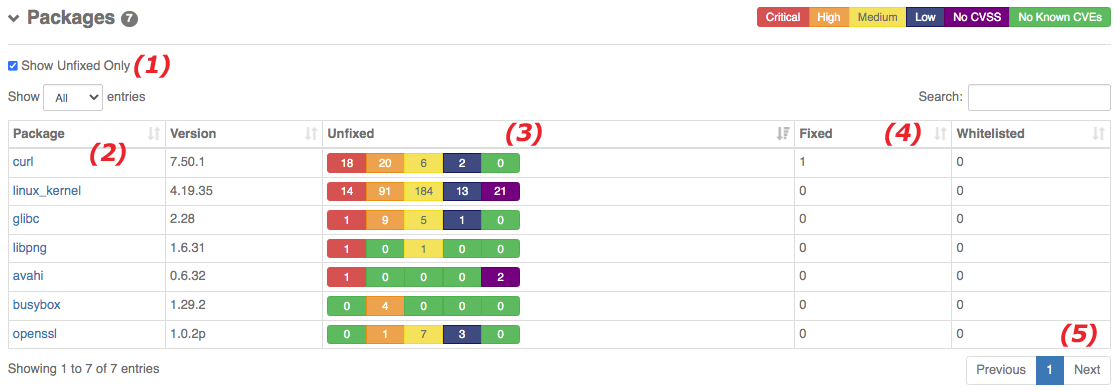
The packages section summarizes the CVEs again, but broken down by package.
- Note the checkbox for Show Unfixed Only.
- The packages are listed here. Clicking on the package names will apply a filter to the CVE section, only showing that package’s CVEs. You can clear the filter using the options in the CVE section.
- You can quickly visualize where the high severity CVEs are located.
- You can also see how many of the known vulnerabilities you have fixed or whitelisted.
- Note that the packages list is paginated.
3. CVEs Section
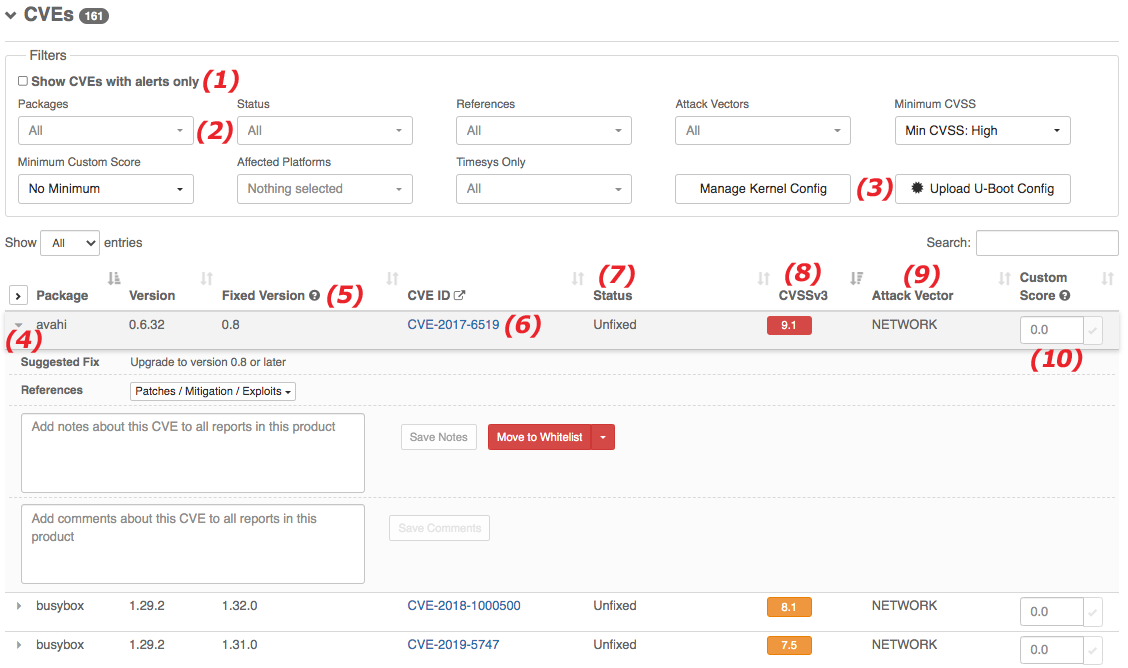
Now we get into the important details. The CVE section will list the vulnerabilities that were found. You can filter this list down to speed up your workflow.
- The “Show CVEs with alerts only” will filter to only CVEs that triggered alerts that you set. These can be based on CVSS score, custom scoring, or package license triggers.
- The filter pulldowns will allow you to narrow down your review of the vulnerabilities. The Minimum CVSS filter may be applied already to your report.
- Kernel Config and U-Boot Config can make a huge impact on your reported vulnerabilities! Try to take advantage of this feature by either using the build integration or adding the config information to your manifest.
- Expand the rows to access suggested fixes, patch links, add notes, and whitelist any CVE you will not be mitigating. For kernel and U-Boot vulnerabilities, config options that will mitigate the vulnerabilities will be shown here.
- The Fixed Version will tell you the minimum package version that includes a fix for the CVE. When no version is given, you’ll have to check the CVE.
- Clicking on the CVE will take you to a Timesys page with more detailed information about that CVE.
- Status will show whether or not the vulnerability is Fixed, Unfixed, or Whitelisted in your manifest.
- This shows the CVSS score for the CVE. CVSSv3 is used when possible.
- Attack Vector will give you the context in which a vulnerability can be exploited.
- You can add custom scoring here to help with your triage.
Need help getting started?
Are you having problems getting your SBOM into Vigiles or have questions and want to see a demo of specific features?
Fill out the form to schedule a complimentary 30-minute Vigiles Quick Start consultation. We’ll be happy to help answer your questions so you can get your vulnerability management process up and running quickly.
* Denotes required field.
Additional Resources
Timesys Vigiles User Guide Videos — YouTube Playlist
Copyright © 2018-2021 Timesys Corporation. All Rights Reserved. Privacy Policy | Cookie Policy | Support Policy | Eula | Terms of Service | Terms of Sale 



All company and product names mentioned and marks and logos used are trademarks and/or registered trademarks of their respective owners.
 Translate
Translate