Top Companies Choose Timesys




With twenty years of embedded software experience, we bridge the skill and resource gap: providing cybersecurity tools and delivering long-term maintenance support for your embedded Linux, RTOS, and Android devices.
BUILD
Custom embedded Linux, Android, and open source OS development
SECURE
Device security for the full product lifecycle, from design to launch and beyond
MAINTAIN
Long-term security updates and maintenance of your Linux OS/BSPs
Security Feature Implementation
VigiShield Secure By Design
Build security into the design of your device by utilizing our embedded experts to implement core security features. This includes: secure boot/chain of trust, device encryption and secure key storage, Over-the-Air (OTA) software updates, hardening, and security audits.
Implementing security early in the design of your device is key to managing its security:
- Reduce the attack surface of your device
- Avoid production delays by securing your software supply chain


Vulnerability Monitoring and Remediation
Vigiles
Manage the growing tsunami of new CVEs (Common Vulnerabilities and Exposures). Detect, filter, triage, and remediate vulnerabilities with the industry’s first Software Composition Analysis (SCA) and CVE monitoring tool optimized for embedded Linux and usable for all open source software.
- Drastically reduce your workload
- Produce an accurate Software Bill of Materials (SBOM)
Long-Term Support
Linux OS and BSP Maintenance
Keep your device secure while in the field with long-term security updates and maintenance. Offload the complex, time-consuming work of OS/BSP maintenance to embedded Linux security experts.
- 60%+ cost reduction for BSP maintenance
- Updates based on your schedule, as often as you need them
- Long-term support for up to ten years and beyond


Embedded Linux/Android OS and BSP Development
Engineering Services and Consulting
Work with embedded platform experts with broad experience across Linux, Android, and RTOSes to help build and secure your custom embedded platforms and custom BSPs. Timesys can help with: custom board bringup; device driver development; kernel upgrade; boot time improvement and performance tuning; manufacturing support for End-of-Line (EOL) Test and programming devices; and more.
- Broad expertise in embedded OS & build systems
- Engage at any stage of product lifecycle
- Work with industry pioneer: founding member of Yocto Project
Test Automation and Remote Access Infrastructure
Embedded Board Farm
Utilize our test automation infrastructure to bring your embedded device into your CI/CT process. Make your boards remotely accessible for collaborative software development, test automation, and debugging from anywhere in the world.
- Use a modern CI/CT system to achieve higher efficiency and quality
- Integrate your favorite test framework onto shared board farm infrastructure, with real hardware
- Minimize cost and project schedule by eliminating hardware access bottlenecks

You’ll be among great company
Timesys is the worldwide choice of the embedded industry.




















































ROBERT THOMPSON
-I.MX ECOSYSTEM MANAGER
AT NXP-
Security is critical for today’s IoT and embedded systems. Medical devices, retail point of sale, and industrial control systems handle sensitive data, so the security of devices used in these applications is essential. We’re partnering with Timesys to highlight best practices for designing and maintaining security in systems using our feature-rich and performance-scalable i.MX applications processors.
AKIRA KOBAYASHI
-PRESIDENT & CEO OF LINEO
SOLUTIONS, INC.-
Developers of embedded systems must ensure their products are secure, or they place their customers at risk Developers of embedded systems must ensure their products are secure, or they place their customers at risk massive commitment of time and resources because of the flood of vulnerabilities. With Vigiles, Timesys is delivering a breakthrough in the automation of vulnerability identification, tracking, analysis and mitigation.
ROY MURDOCH
-VDC RESEARCH-
Security is at the forefront of today’s IoT issues as the discovery of new vulnerabilities and the rate of attacks continue to escalate. Improving security is becoming especially critical for IoT and IIoT devices because of the rapid expansion of deployments combined with the rise in botnet, bricking and other attacks against these smart devices. Timesys is bringing to market a timely solution, designed to make these devices more secure and maintain that improved security posture into the future.
SEE THE SOLUTION YOU NEED?
Start the Conversation
Stop worrying about how you are going to find the engineering time and in-house expertise to give your product the professional architecture and security attention it needs.
Learn More
Case Study
Secure Boot in Industrial Welding
Timesys’ security expertise helps manufacturer of industrial welding products deliver a secure IoT gateway for its factory installed products
Webinar
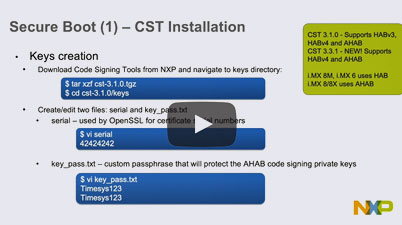
Establishing secure boot and chain of trust
Explore the “Secure by Design” approach to software security for embedded systems using NXP i.MX processors.
Blog
Trusted Software Development Using OP-TEE
How end users can leverage open source software to safely deploy applications that require handling confidential information