Thank you for your interest in the Timesys – NXP “Secure by Design” webinar series
Click on any link below to jump to the webinar description and link to the on-demand page where you can watch the recording and download the presentation.
Securing Embedded Linux Devices: Pitfalls to Avoid
The pressure to reduce time-to-market for embedded devices often means that security does not receive the attention it deserves.
But as customers demand more secure products and as reports of new vulnerabilities surge, security must be front and center in our product design and maintenance processes.
Join this webinar to explore the proven best practices for designing and maintaining secure products, common security pitfalls, and tips for hardening embedded Linux devices.
We will discuss:
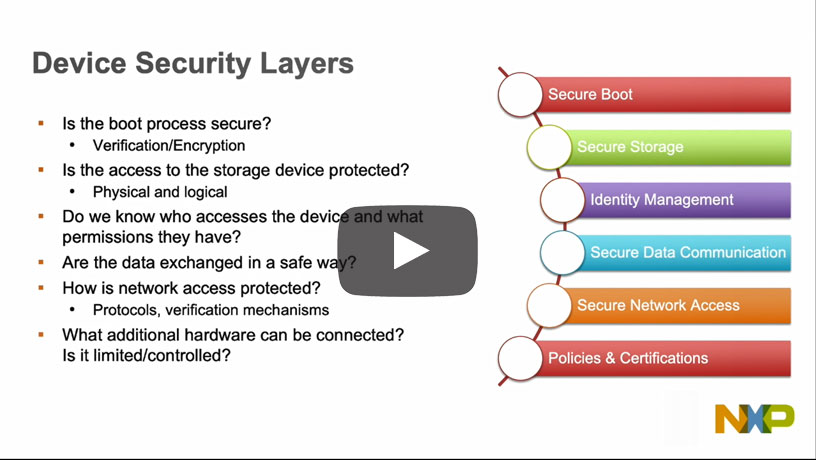
- Evaluating security features in NXP processors, Linux kernel and other Open Source Software components to meet product security requirements.
- Avoiding common security pitfalls including: incorporating third-party software with unknown vulnerability exposure; not running static code analysis tools to find potential vulnerabilities; failing to address security in design stages to meet end-product requirements and certifications; not adequately hardening devices; running ineffective security maintenance and update processes.
- Leveraging open source security measures including: “Secure by Design” OS features: secure boot; chain of trust; device encryption; OP-TEE; secure key storage.
- Hardening devices including: access control; secure open source software configurations; login and port controls; secure IoT device network connections; IoT device authentication
- Maintaining security including: vulnerability monitoring and remediation; secure OTA updates to address vulnerabilities in the field; security audit logs, key revocation and security auditing.
Software integrity and data confidentiality: Establishing secure boot and chain of trust on i.MX processors
High-performance, power-efficient processors now can bring “smart” capabilities to a rapidly growing range of connected devices. These capabilities are driving innovation in embedded systems for automotive, medical, aerospace, wearables, IoT, industrial IoT and many other applications.
But as smart connected systems are deployed more widely, ensuring the security of these systems and the data they process is ever more critical. Checking the authenticity of software running on these remote connected devices is paramount to ensuring their security.
To achieve this, an essential best practice is to establish secure boot and chain of trust in the software running on your embedded Linux systems.
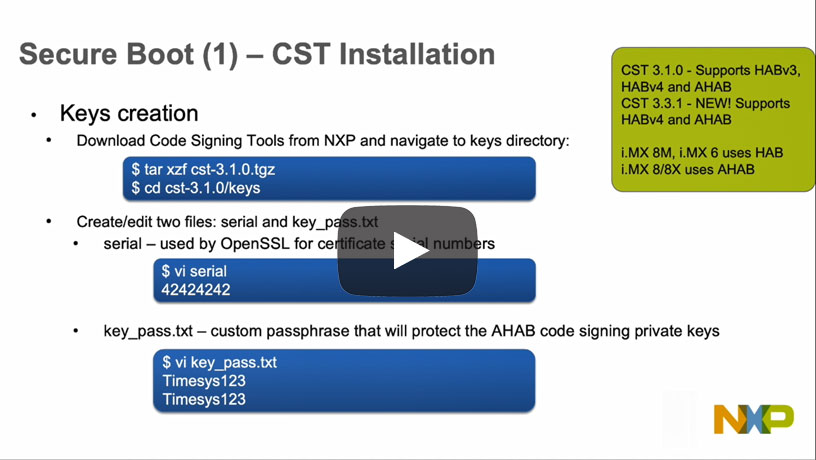
This presentation will explore this “Secure by Design” approach to software security for embedded systems using NXP i.MX processors, including:
- Defining security requirements such as maintaining software integrity and ensuring data on your devices is protected and confidential.
- How secure boot ensures only authenticated software runs on your device, protecting against the execution of malicious code.
- How establishing a chain of trust can ensure software authenticity all the way from the bootloader to user applications.
- Techniques such as verifying the bootloader on NXP i.MX processors, kernel verification, root filesystem verification, and file system integration and secure key storage.
Trusted Execution Environment: Getting started with OP-TEE on i.MX processors
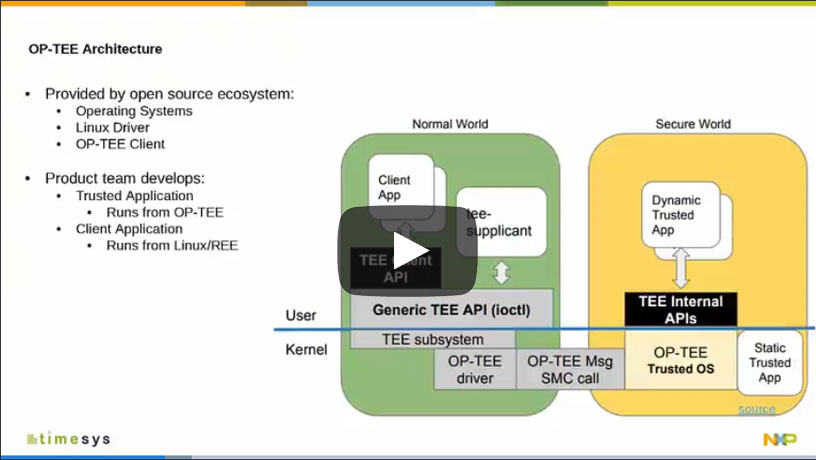
A Trusted Execution Environment (TEE) isolates sensitive data and processes from non-secure processes, creating secure or trusted zones and non-secure, non-trusted zones in your embedded system product.
Arm offers TrustZone technology for creating a secure, isolated operating environment and NXP’s i.MX processors leverage this technology to provide the foundation for a TEE. But implementation of the TEE takes place in the software you develop for your embedded system products.
This webinar will explore how to get started with using a TEE in your projects using i.MX processors.
We Will Discuss:
- An overview of TEE and the “normal world” and “secure world” partitioning.
- Example use cases for leveraging TEE to to secure functionality that requires it.
- A look at Open Source Portable TEE, OP-TEE, and how to leverage i.MX hardware security features from OP-TEE.
- Tips and best practices for accelerating secure product development with TEE.
Linux Kernel Security: Overview of Security Features and Hardening
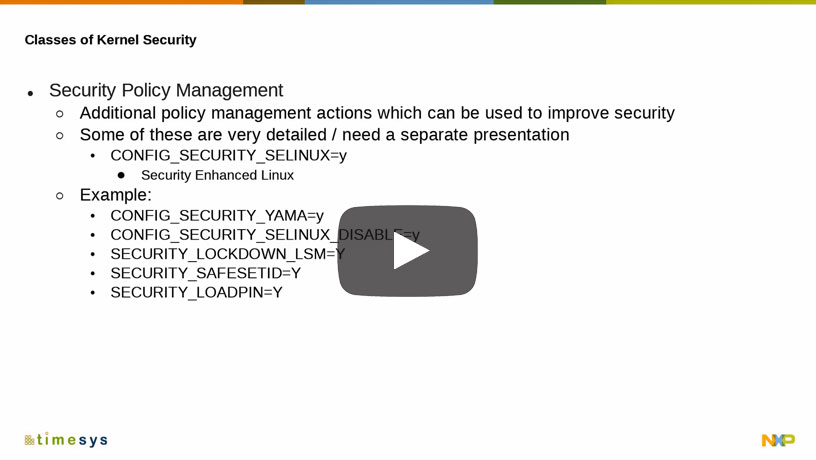
An essential part of bringing secure embedded system products to market is to ensure that your Linux kernel’s configuration can be strengthened to protect against security exploits. This is sometimes referred to as hardening, or in this context, kernel configuration hardening.
This training will feature an overview of how to secure the Linux kernel in your products and decrease the risk of a damaging attack.
What You Will Learn:
- Kernel configuration options to mitigate known exploits, to enable security features and to disable unneeded configuration options
- Memory protection steps to prevent exploits and security issues such as stack overflow, heap overflow, user copy protection, and information exposure
- Steps to reduce your device’s attack surface with options that minimize the amount of information exposure and compiled-firmware attack surface
- Tools that can simplify and accelerate your kernel security analysis
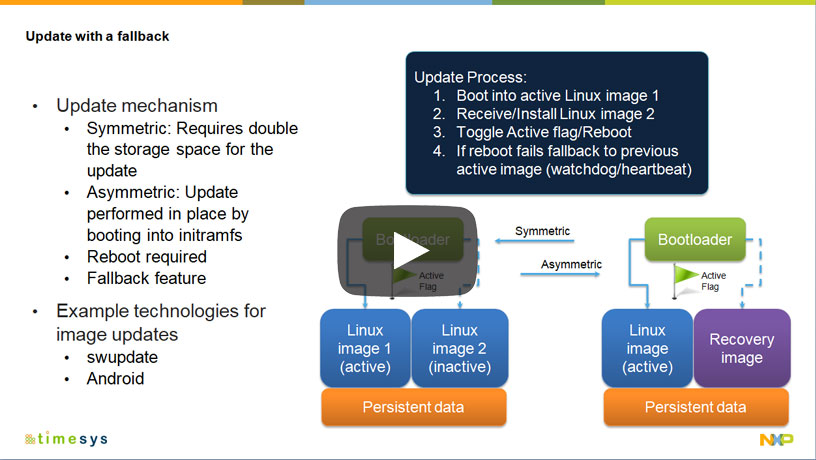
Secure the Edge: Secure Software Updates — Designing OTA Updates For Secure Embedded Linux Systems
Building a secure embedded Linux-based device is a good start. But maintaining a strong security posture throughout your device’s production deployment and long-term maintenance is just as critical.
As the number of software vulnerabilities has exploded, customers are increasingly at risk of a data breach exploit if embedded system software is not updated to the latest available security fixes. At the same time, the update process must be secure to ensure it does not become an attack vector itself.
This webinar explores the most commonly used approaches to field software maintenance and the design considerations for ensuring efficient remote updates.
We’ll discuss:
- Field updates of the software on your embedded systems, with Over-the-Air (OTA) and person-assisted processes
- Incremental updates, full OS updates and patching and how they fit in your product and maintenance processes.
- Signing of packages and update images, server authentication and other key considerations for securely deploying updates and denying unauthorized software installs.