Need to get a handle on CVEs affecting your products? Willing to share feedback for our internal research? See if you qualify for our user trial. $50 gift card or donation for eligible participants.
Timesys Vigiles® Vulnerability Management Suite: Best-in-Class Security for Embedded Linux Devices
- Better Data: Up to 40% more accurate than National Vulnerability Database (NVD) data alone
- Superior Insights: Save up to 75% in investigation time and stop chasing ‘Vulnerability Ghosts’ & false positives
- Key Process Improvements: Up to 90% reduction in end-to-end security maintenance tasks compared to manual processes
- Easy Compliance: Order of magnitude reduction in level of effort to comply with industry and customer-specific security requirements and specifications, government regulations, and security certifications
- Start Immediately: Integrated with industry standard Yocto, Buildroot, and Timesys Factory build systems
New Security Challenges Require New Solutions
Are customers reporting cybersecurity issues with your products before you know about them?
Are they asking when you will have them fixed?
Is your new security team rolling out new cybersecurity policies but you have no tools to comply?
Are customers wondering why you don’t publish cybersecurity policies like competitors do?
Get ahead of your customers’ requirements and competition with Timesys Vigiles.
What is Vigiles Vulnerability Management?
Like the famed ancient Roman city watchmen for which it is named, Vigiles is a tool that constantly watches to keep things secure.
The Timesys Vigiles suite of tools enables you to generate and analyze a Software Bill of Materials (SBOM) for your embedded system software built on Linux.
Vigiles is optimized for embedded systems and provides a complete vulnerability lifecycle management tool: discovery, prioritization, triaging, remediation, compliance and on-going monitoring/alerts.
Why Vigiles?

First SCA solution optimized for embedded systems, native integration with Yocto, Buildroot, Timesys Factory.

Automatically generates remediation information including patches and updates for your software components.

Removes any vulnerabilities affecting features not being used by your product, saving you valuable time.

Monitors for your Linux Kernel and U-Boot configuration as well as packages and libraries used in your specific project.

Filters reported vulnerabilities so you can focus on only those that affect the exact Software Bill of Materials (SBOM) used to produce the bootable firmware images on your product.

Enables automatic alerts for non-authorized license type and for CVEs exceeding CVSS score threshold
Why Timesys Vigiles is the industry’s choice for embedded Linux security
[avartanslider alias=’slider11′]
The Timesys Vigiles Vulnerability Management Suite is a best-in-class Software Composition Analysis (SCA) and vulnerability management solution optimized for embedded systems built on top of the Linux operating system.
Vigiles will reveal your exposure for every product and software release, and provide clear engineering guidance on how to remediate vulnerabilities. Now your customers can receive software updates sooner and stay secure throughout the lifecycle.
 FREE (Free, basic version)
FREE (Free, basic version)
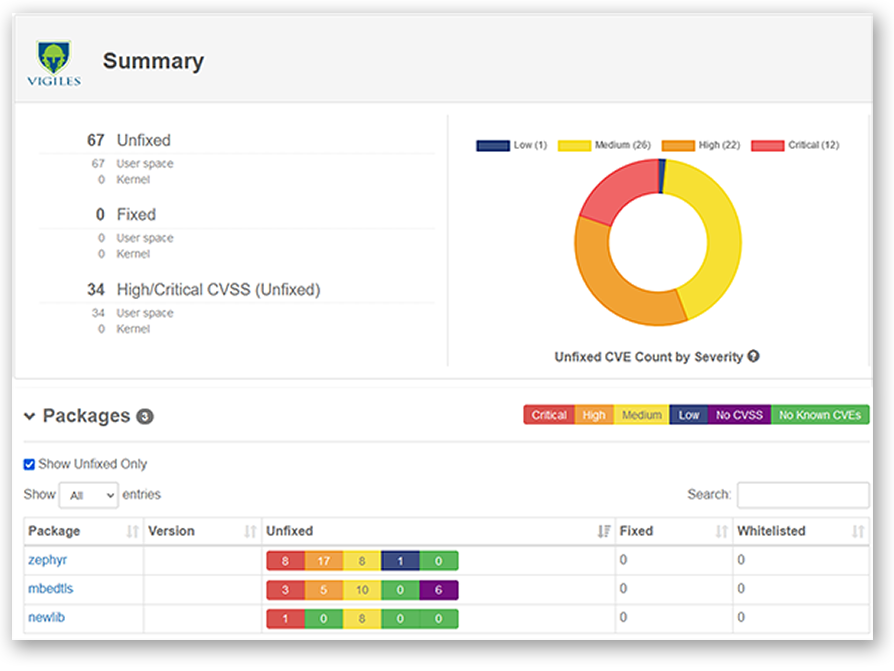
Automatically monitors thousands of reported vulnerabilities and provides unique targeted vulnerability detection for your specific product components, including alerts of new vulnerabilities, summaries of severities and status, and on-demand reports for your projects
 PLUS
PLUS
Gives you all of the Free version’s vulnerability monitoring features along with powerful vulnerability analysis, triage, and collaboration tools, to enable your team to rapidly prioritize, assess and mitigate security issues
 PRIME
PRIME
Features all the monitoring and mitigation tools of Free and Plus, enhanced with unique patch notification features, automatically generating recommended fixes based on identified vulnerabilities specific to product components, augmented by detailed version analysis and tracking across all branches
See Vigiles in action
Watch Timesys Vigiles Advanced Software Composition Analysis (SCA) and Vulnerability Management Tools Video
Watch Timesys Vigiles Advanced Software Composition Analysis (SCA) and Vulnerability Management Tools Video

Timesys Vigiles keeps products secure throughout their lifecycles

Part of your processes
Vigiles creates a well-defined, efficient, repeatable and scalable process workflow for developer-driven product security, integrated with Yocto, Buildroot and Timesys Factory.

See and track exposure
You receive notification of only those vulnerabilities affecting your software. Reporting tools let you track vulnerabilities over time and monitor remediation progress

Automatic suggested fixes
Vigiles automatically notifies you of “suggested fixes” such as patches or updates of components that will remediate vulnerabilities.

Access CVE details easily
Powerful dashboard enables you to see, investigate, filter, and prioritize vulnerabilities.

Always know what is affected
Subscribe to notifications for all your software manifests across all versions and branches.

Remain in control
Continuously monitor old and new vulnerabilities as your products change, for more secure products throughout the lifecycle.
The industry’s most secure embedded system products
Timesys customers are market-leading device makers that develop more secure products and bring them to market more quickly thanks to Timesys’ unique Secure By Design and Stay Secure solutions. Their products are designed to be more secure and they remain secure, keeping security exploit risk low throughout the product lifecycle.
Check out some of the case studies to see how these device makers avoid making trade-offs between security and time-to-market:
Related Resources
Videos
Timesys Vigiles User Guide Videos — YouTube Playlist
Video

 FREE
FREE