Vigiles subscriptions are annual, with three tiers to choose from.
Learn more about Timesys Vigiles Vulnerability Management Suite
Compare Vigiles Versions

SBOM MANAGER
SBOM Manager version provides SBOM management and generation tools in industry-standard CycloneDX and SPDX formats, comparison of SBOM changes between builds and releases, tracking, monitoring, and more for multiple SBOMs
PRIME
All the features of the SBOM Manager version plus CVE monitoring for SBOMs, collaboration tools for CVE triage and mitigation, advanced filtering, detailed notifications, advanced reporting tools, patch notification and management features, links to related Linux kernel patches, OSS fixed version notifications, and more.
ENTERPRISE
All the features of the SBOM Manager and Prime versions, with single sign-on compatibility, powerful group administration functionality, role-based access control, and hosting with remote CVE database updates.
Yearly subscription. Long-term subscriptions also available. Contact sales for more details.
Yearly subscription. Long-term subscriptions also available. Contact sales for more details.
Yearly subscription. Long-term subscriptions also available. Contact sales for more details.
SBOMs Generation and Management
Track multiple Software Bill of Materials (SBOMs)/manifests
Ability to load product SBOM listing your software components and versions
Upload/Ingest your Software Bill of Materials (SBOM) or create one using the “SBOM Creator”/Web wizard



Build system support: Yocto, Buildroot, PetaLinux, Wind River Linux, PTXdist, OpenWrt, and Timesys Factory



Export your Software Bill of Materials (SBOM) in SPDX, CycloneDX, SPDX-Lite format



Software Bill of Materials/Manifest editor and revision management



Convert and Download SBOMs into different formats



Comparison of changes between builds/releases (SBOM/manifest difference)



Standards and Compliance
Software License information (Yocto and Buildroot only)



Meet NTIA Compliance Regulations and White House Mandates such as 14028 EO and IMDRF N60
Meet FDA Cybersecurity in Medical Devices requirements, NTIA minimum compliance requirements for Software Bill of Materials, Executive Order 14028 requirements, and other regulations and compliance mandates with accurate SBOMs and CVE management from Vigiles.



CVEs Accurate Detection & Analysis
CVE summary by severity, status, and software package



Early CVE notification


Accurate Curated CVE Database


Comparison of reports for new and changed CVEs


Push notifications of vulnerabilities
On-demand CVE report generation via Web


On-demand CVE report generation via command line
Download CVE reports in different formats such as CSV, XLSX, and PDF


CVEs Triage & Prioritization
Filter reports based on kernel and U-Boot configuration


Filter based on CVEs Affecting your Components or Status
Filter reports by severity (CVSS) score or attack vector


Custom vulnerability score/prioritization and filtering


Team Collaboration & Workflow
SBOM collaboration



Access to free Vigiles Quick Start Education Program



Automatic alerts for non-authorized license type and for CVEs exceeding CVSS score threshold


Robust Google-Style CVE search tool for Timesys curated CVE database


CVE report history with CVE trend plot


CVE report sharing


Team sharing and CVE mitigation collaboration tools


Continuously track specific issues and CVE status changes


Integration with Jira, Nucleus Security, and other tools to further streamline vulnerability issue tracking and management


Application Programming Interface (API) Toolkit


Single Sign-On

Groups Functionality

Role-based access control

Vulnerability Mitigation and Patching
Intelligently Whitelist already-reviewed CVEs across SBOMs to streamline reviews


Reference links to available patches, mitigation, and exploits


Link to mainline kernel fix/patch commit for Linux kernel CVEs


Minimum kernel version with a fix/patch for a kernel CVE


Suggested fix/patch for OSS CVE remediation


Frequently Asked Questions (FAQs)
Product Features
What is the difference between Vigiles SBOM Manager, Prime and Enterprise?
Vigiles SBOM Manager offers Software Bill of Materials (SBOM) management and generation tools in industry-standard CycloneDX and SPDX formats, comparison of SBOM changes between builds and releases, and tracking, monitoring, and team collaboration for multiple SBOMs.
Vigiles Prime provides everything that SBOM Manager provides along with vulnerability monitoring and more detailed reports for an unlimited number of SBOMs, and collaboration and communication tools to enable your team to analyze and work on mitigation for vulnerabilities. You also get Patch Notification and Management features, identifying patches and minimum versions to secure the software components that are identified in your manifests.
Vigiles Enterprise gives you single sign-on capability, an expanded group control function to collaborate within teams more easily while controlling access to work, and expanded role-based access control. All hosted on-premises so you can keep your triage efforts inside of your own network.
How does Patch Notification & Management in Vigiles Prime help with vulnerability management?
Without Vigiles Prime patch management, your triage and mitigation activities will include identifying each component supplier and researching which version of a component has an available fix for a given vulnerability, if one is even available.
In contrast, Vigiles Prime patch management will automatically notify you of a patch associated with a given vulnerability for your specific components. Vigiles Prime will give you a direct link to the download for the patch. Further, Vigiles Prime will provide you with details on the minimum versions of libraries or packages and kernels that address the identified vulnerability.
Our analysis shows that Vigiles can cut your vulnerability identification and mitigation process cycles by 90 percent when compared with manual detection, investigation, and mitigation.
What are Triage Collaboration and Mitigation Tools in Prime and Enterprise?
For example, a team assigned to review a set of vulnerabilities might assign some team members to conduct impact analysis. Those team members can communicate quickly and easily about their evaluation of the security risks posed by specific vulnerabilities.
Other members may focus on high severity vulnerabilities to investigate expedited mitigation options, sharing their findings to weigh options and accelerate the response and fix.
Throughout these processes, some vulnerabilities may be whitelisted, which means they are tagged as acknowledged and in process or fixed. That way they do not clutter up the broader evaluation of inbound vulnerabilities or the mitigation workflows.
Along with flexible filtering, dashboarding, and reporting features, these collaboration tools can significantly cut the time your team spends on understanding the impact of a vulnerability and fixing it.
How do I upgrade to Prime?
Is Vigiles open source?
One part of Vigiles collects the software manifest from a Yocto project and is licensed under MIT license with Timesys copyrights (see: https://github.com/TimesysGit/meta-timesys/tree/zeus).
The other part consists of the Vigiles scanner, backend database and user interface. This part of Vigiles is a Timesys proprietary product.
Does Vigiles only support Yocto or does it support other build systems? Are custom Linux kernel, crosstools and bootloaders also supported?
Using the Vigiles UI, you can upload software manifests from Yocto, Buildroot and Factory. In addition, Vigiles supports .csv format, so you can generate a software manifest from any other build system and format it as a .csv spreadsheet that you can upload. We provide guidance on creating a Vigiles .csv manifest here: https://linuxlink.timesys.com/docs/wiki/engineering/VigilesCSV.
You can also create your software manifest from scratch entirely online using the Vigiles “Create Manifest” UI.
Can Vigiles be used with any BSP or processor?
Currently, we use Linux kernel 4.9 in our project. Can it be scanned using Vigiles or does the kernel need to be a newer version?
With older kernel versions, you should expect to see more vulnerabilities in the Vigiles report. In general, we recommend that our customers use a recent Long Term Support (LTS) version of the Linux kernel. Because security fixes get backported by LTS kernel maintainers, using a recent LTS version of the Linux kernel will allow you to leverage those backports in your BSP/product.
What is a SBOM or product manifest?
An SBOM (Software Bill of Materials) or product manifest is the inventory of your product’s software components and the versions in your design loaded into Vigiles for security monitoring.
Do I need to manually load my SBOM each time a report is generated?
Vigiles does not require you to upload the SBOM each time it is run. In a typical Yocto build environment, the Vigiles Yocto layer will extract the SBOM from your source code.
How are Vigiles results presented? Are the reports exportable (json/xml) for integration into company-wide issue trackers?
In the upcoming Vigiles release, you will also have the ability to get reports via JSON directly in your build system. This will provide further integration into your company-wide issue tracker.
Is there a limit to the number of the projects you can have in Vigiles?
How is Vigiles different from other vulnerability scanners including Black Duck?
- Tracks CVEs already fixed in Yocto/Buildroot, letting you/your team focus on vulnerabilities that need to be fixed.
- Enables up to 4x reduction in CVE review with kernel and U-Boot configuration-based filtering.
- Provides superior vulnerability reporting with fewer false positives.
- Provides links to patches and commits, reducing time to needed address/mitigate vulnerabilities.
- Features an advanced filtering capability, helping you/your team to prioritize and focus on only the vulnerabilities that matter.
In addition,Vigiles customers have access to the Timesys TRST Security team for help with any CVE questions as well as access to a Managed BSP Maintenance Service option for those who do not want to fix the vulnerabilities themselves.
Does Vigiles support Android security patches?
For the Android Open Source Project components from Google, use the security tracking bulletin from Google (https://source.android.com/security/bulletin).
Do Vigiles and Linux Test Project (LTP) overlap?
Vigiles monitors vulnerabilities for the entire Linux BSP including the Linux kernel, bootloader and userspace packages, and LTP helps with verifying/testing Linux feature functionality. Therefore, you can use Vigiles to identify CVEs and available fixes, and then once you and your team go through triaging and fix implementation, you can run LTP to verify Linux functionality.
Is it possible to run Vigiles on a device not connected to the Internet?
Vigiles works by extracting package/version information from the build system Yocto/Buildroot) or by the user generating/uploading a Software BOM CSV file to Vigiles. Vigiles then compares the list of packages/versions against a Timesys-curated vulnerability database and generates a web report accessible only by the end user and/or user’s team.
Currently, Vigiles is a hosted/cloud only solution; we do not provide an on-premises version of Vigiles that can be on your network without internet access. However, we do plan to provide an on-premises version later this year.
Technology
Can I have multiple Vigiles seat tiers at the same time, such as one in Vigiles SBOM Manager and another in Vigiles Prime?
Technology
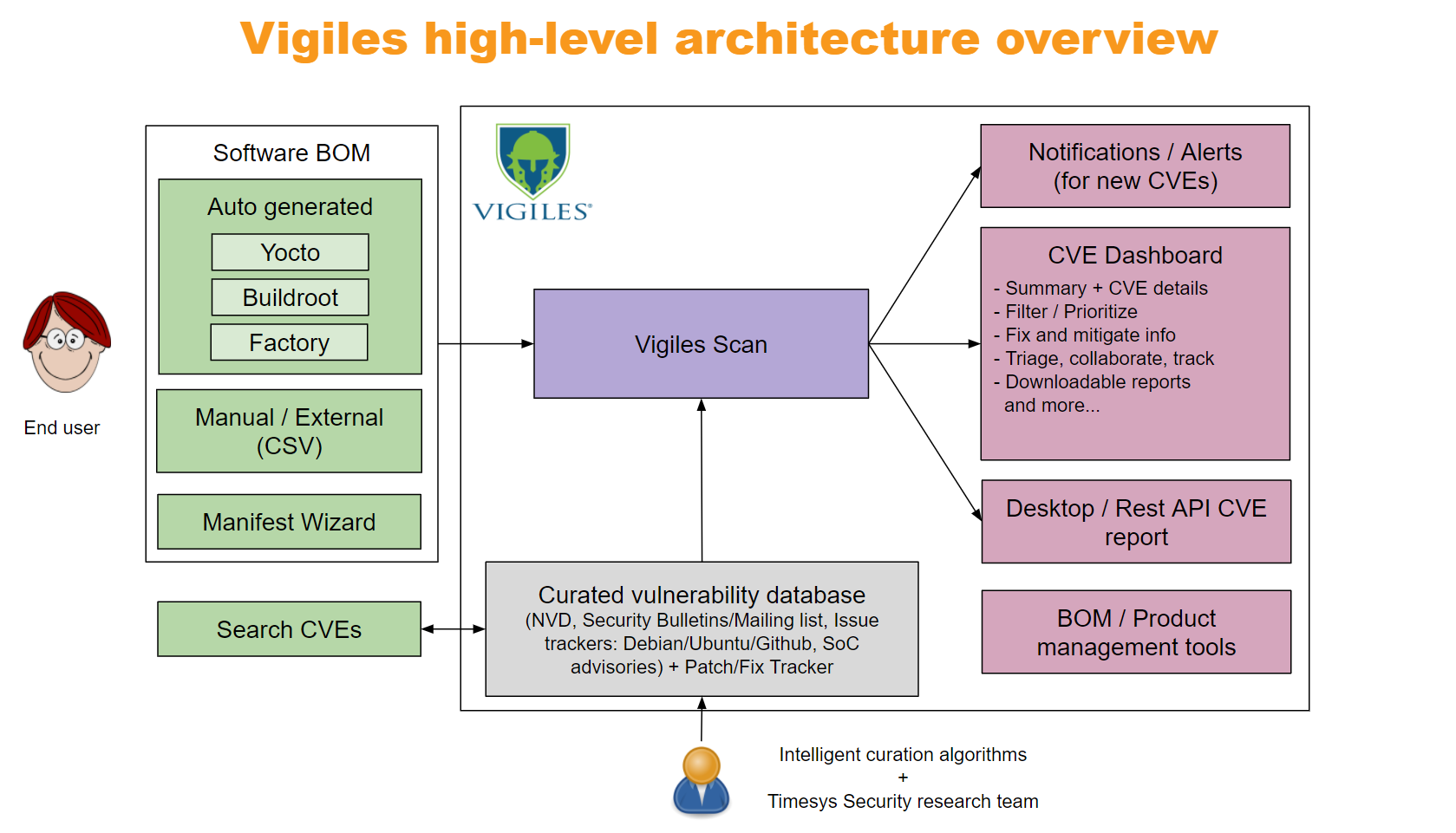
What is Timesys Vigiles?
Vigiles is a software composition analysis and vulnerability management solution optimized for embedded Linux that combines SBOM management with the ability to track Common Vulnerabilities and Exposures (CVEs), providing end-to-end vulnerability management, while improving on the CVE data publicly available from the National Vulnerability Database (NVD).
Technology
How does it work? How does Vigiles determine which CVEs to report?
For a particular CVE, there is a unique name for the specific software or hardware that is affected. This scheme is called Common Platform Enumeration (CPE), and it’s used for mapping a CVE to a product name and version. Most commercial and open source tools use CPE.
If this hardware or software CPE appears in a client’s Software Bill of Materials (SBOM), then Vigiles pulls the data for the corresponding CVEs. The SBOM is automatically generated for Yocto and Buildroot.
Of the approximate 350 new CVEs announced each week, is this just the number of CVEs reported against the Linux kernel mainline?
On average, you should expect that approximately 10 CVEs/month will directly apply to your embedded Linux product. And many of these issues will indeed be reported for the Linux kernel itself.
Can you get false positives?
This can be due to CPE data quality issues (like incorrect product names or version information), incorrect SBOM information (name/version number), or delays in a CVE being published in the NVD.
Timesys takes a number of steps to improve coverage and reduce false positives; see the next question and answer for further details.
How does Vigiles filter out false positives?
Then, Vigiles relies on our curated CVE database during the scanning process. In addition, Vigiles takes into account any filters you may applied such as the Linux kernel configuration and U-Boot configuration filters, along with factoring in any CVE patches already applied, resulting in a highly accurate security vulnerability report.
How does Vigiles improve upon info from the National Vulnerability Database (NVD)?
Timesys’ security team has error detection mechanisms in place via our Linux OS/BSP Maintenance service, customer feedback, and upstream Yocto patch submissions. Using this info, the security team manually analyzes incorrect CVEs and updates it in our systems. We also cross-verify our database with Upstream mailing list, issue trackers, security bulletins, Debian/Ubuntu/RedHat security trackers, SoC vendor advisories.
Additionally, we’ve created intelligent curation algorithms for the Linux kernel and u-boot that run on a nightly basis. We automatically update our curated database with fix commit and backports using git.
Finally, we minimize reporting delays. By augmenting our database with information from multiple feeds, we can notify our customers of CVEs not yet reported by the NVD — sometimes up to four weeks earlier!
Does Vigiles have a way to catch errors like typos or missing mappings?
However, Timesys cannot guarantee that Vigiles is entirely free from errors, defects, or bugs, currently known or unknown.
Can Vigiles be used to report vulnerabilities in userspace applications?
Vigiles does not scan your BSP source code for code injections. Vigiles reports on the version of individual software packages you are using in your BSP and a list of patches that are applied on top.
Therefore, if CVEs are reported against application software you’ve used, Vigiles will be able to provide you with information. However, if you are using an in-house developed proprietary application for which CVEs are not reported, Vigiles will not be able to provide any vulnerability information.
If we have made custom changes in the kernel driver, would Vigiles be able to report on related vulnerabilities?
If you modify the driver before applying a CVE patch, you will have to adjust the CVE patch to apply on top of your changes. Therefore, it is recommended to first apply a CVE patch and then make customizations. This would possibly require adjustments to your customization patch.
What information is collected when I upload my SBOM for security monitoring?
Timesys Vigiles only collects package/recipe names, version, patches applied (if any), and build system version information. This information will only be shared with members of your team.
Timesys Vigiles does not require you to upload your product source code.
What does Timesys do with the information in my confidential product software SBOM?
We currently don’t do anything with the customer information uploaded to Vigiles. Your product SBOM(s) will remain in your Vigiles account for as long as you need.
When no longer needed, you can delete the information you’ve uploaded yourself or ask us to delete it for you.
What security measures has Timesys implemented to ensure my product software SBOM does not get shared with other Vigiles users?
By default, all CVE links are private and are not accessible to other users based on login authentication.
What assurances can Timesys provide that my product software SBOM information will not be hacked or otherwise leaked from Vigiles?
Timesys stores all SBOM information in an encrypted disk.
How does Vigiles handle third-party source code that is included, but not shown in Yocto recipes? For example, QtWebEngine has Chromium source code included and hence is subject to the same CVEs as Chromium, with a number of proprietary patches. Will Vigiles report on these CVEs when including QtWebEngine?
Applicability of a CVE reported on one package to another requires engineering triaging. If maintainers of the Qt package do this, CVEs will be marked by them as applicable.
We provide a BSP Maintenance service where our engineering team does the triaging of CVEs. This service could be also used to triage Chromium CVEs for QtWebEngine.
How does the vulnerability report get updated to our project account in Vigiles? Does it update automatically or do we/does the developer need to update the report as necessary?
To obtain an updated Vigiles vulnerability report, you have several options including:
- You can push the software SBOM to your Vigiles account every time you run a Yocto build or request a security report using YoctoBitBake commands. When you rerun the build on the same Yocto image, the software SBOM can be updated in place. This way, if you add another package to your BSP, it gets reflected in the same product Vigiles report. Because Vigiles stores the older versions of the SBOM, you can always go back to view and/or generate reports for older SBOMs.
- You can subscribe to notifications on new vulnerabilities reported against a SBOM. Once a SBOM is in Vigiles, you can choose to receive vulnerability notifications daily, weekly or monthly. Vigiles will automatically run a security scan and email you the information based on your cadence preference.
- You have the ability to upload either a new SBOM or an updated version of a SBOM at any time using the Vigiles UI.
Using Vigiles and this product model, who is responsible for fixing/mitigating a vulnerability?
The process of triaging identified CVEs and how they apply to your product, the decision to apply available fixes, the implementation of fixes, and the building and testing of the modified Linux product image is the responsibility of you/your engineering team. Additionally, suggested fixes, patch, and mitigation information is not verified by Timesys.
For those wanting to offload this task, we offer managed Linux OS and BSP Maintenance.
I already have Black Duck. Do I really need Vigiles too?
What about vulnerabilities not in the CVE dictionary?
To achieve the most comprehensive vulnerability data, Timesys recommends that you run static analysis tools, fuzzing tools, monitor mailing lists, issue trackers, and security bulletins / advisories.
How can I report an issue?
Glossary of Terms
CNA: CVE Numbering Authorities are organizations from around the world that are authorized to assign CVE IDs to vulnerabilities affecting products within their distinct, agreed-upon scope, for inclusion in first-time public announcements of new vulnerabilities. (Source)
CPE: Common Platform Enumeration is a structured naming scheme for information technology systems, software, and packages. Based upon the generic syntax for Uniform Resource Identifiers (URI), CPE includes a formal name format, a method for checking names against a system, and a description format for binding text and tests to a name. (Source)
CVE: Common Vulnerabilities and Exposures
A vulnerability is a weakness in the computational logic (e.g., code) found in software and hardware components that, when exploited, results in a negative impact to confidentiality, integrity, or availability. Mitigation of the vulnerabilities in this context typically involves coding changes, but could also include specification changes or even specification deprecations (e.g., removal of affected protocols or functionality in their entirety). (Source)
A vulnerability that has been assigned a CVE identifier number is colloquially referred to as a CVE.
NVD: The National Vulnerability Database is the U.S. government repository of standards based vulnerability management data represented using the Security Content Automation Protocol (SCAP). This data enables automation of vulnerability management, security measurement, and compliance. The NVD includes databases of security checklist references, security-related software flaws, misconfigurations, product names, and impact metrics. (Source)
