[DISPLAY_ULTIMATE_SOCIAL_ICONS]
Log4j has set the security world ablaze. With the first vulnerability (CVE-2021-44228) ranked with a CVSS score of 10 — as high as the scale goes — everyone is paying attention.
It’s true that the embedded world appears to be largely unaffected: having reviewed nearly 50,000 Software Bill of Materials (SBOMs), we found that less than .05% of those reviewed use log4j. That said, there are still some major lessons to be learned from this historic attack.
- Have an accurate SBOM
An accurate Software Bill of Materials (SBOM) is your best friend when working in vulnerability management. When news of a new CVE breaks, the quickest way to know whether your device has been affected is to have an accurate SBOM and scan it to determine if you need to take action. And it’s not just a nice-to-have — providing a purchaser with an SBOM is included as part of an executive order from President Biden earlier this year to improve the United States’ cybersecurity. - Track vulnerability lists
The National Vulnerability Database (NVD) is the largest source for vulnerability tracking, but it’s not the only one, nor is it always quickly updated. Tracking and cross-referencing multiple vulnerability lists is the best way to stay ahead of CVEs. Additional places to track CVE information include but are not limited to: Upstream mailing list, issue trackers, security bulletins, Debian/Ubuntu/RedHat security trackers, and SoC vendor advisories. - Monitor consistently
An accurate SBOM and knowing which lists to follow are all well and good, but only if you monitor the lists consistently. With approximately 350 new CVEs every week, they must be constantly monitored, ideally with alerts set up for the most critical CVEs.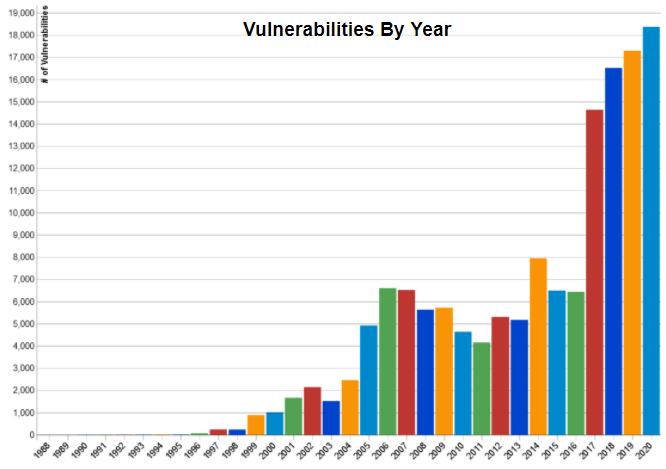
- Consider specialized tools to give you an advantage
Once you know you’ve been affected by a CVE, the work has just begun. How critical is it? Is there a patch? What CVEs need to be taken care of first? You can find a wide variety of tools for tracking, filtering, triaging, and even remediating vulnerabilities — all of which are needed to keep you one step ahead of cyber attacks. You can find an excellent list of Software Composition Analysis (SCA) tools with real customer reviews from Gartner here. - Have a response plan ready
Log4j caught a lot of companies by surprise. If this vulnerability has taught us anything, it’s that we need to be ready to respond when — not if — the next one strikes. When the news of the next major vulnerability hits, will you be scrambling for a solution, or will an early alert from your system mean you’re already applying fixes and protecting your customers?
There are plenty of security scanning tools available on the market, but Timesys Vigiles is the only vulnerability monitoring and remediation tool optimized for embedded. With Vigiles’ curated CVE database, continuous security feed based on your SBOM, powerful filtering, and easy triage tools, it puts you ahead of the curve and poised to take action.
Don’t get blindsided by the next major CVE — try a free 30 day trial of Vigiles Prime today.
[DISPLAY_ULTIMATE_SOCIAL_ICONS]
About Timesys
Timesys has extensive experience with embedded system development and lifecycle management. Timesys has been instrumental in working with global leader semiconductor manufacturers with smart, quick and quality solutions for highly complex systems with accelerated product innovation and multiple product variants.