As discussed in last week’s posting, security often ends up taking a backseat to other considerations when you are bringing products to market or supporting ones already in production deployment.
Product managers often are faced with delivering baseline product functionality and dealing with constraints around timelines and budget. That means broader security considerations fall out of the product when these constraints force trade-offs and fundamental product requirements take priority.
The end result is that many hundreds of products are exposed to today’s massively heightened cybersecurity threat environment without an adequate security posture. That can lead to breaches in customer environments and liability for system suppliers.
Often, the vulnerabilities don’t become visible until a security breach has occurred, followed by the mad scramble to fix the issue and mitigate the damage. Such a reactive approach to security is simply bad product management.
Fast, Fully Featured, Within Budget … and Secure
In our work with developers of embedded systems using open source software, we have seen many projects where product managers make an art of managing trade-offs.
These projects show that security does not have to be sacrificed to other priorities like time-to-market and feature scope.
One of the ways that product managers avoid or lessen the impact of security trade-offs is to create a standing security management process and build it on automated tools that can reduce the time and resources consumed by certain tasks.
Those secure product management best practices are what our Vigiles Security Vulnerability and Patch Notification service is built on.
Vigiles automates steps in vulnerability scanning, vulnerability management, patch management and CVE tracking to make them part of a simple, repeatable and efficient product security review process.
Here are four main steps of an effective product security review process that minimizes the constraint trade-offs, enables you to bring more secure products to market, and maintains strong security throughout the product lifecycle.
1. Component & vulnerability scanning
At the simplest level, vulnerability scanning is really a matching game, sifting through the flood of vulnerabilities to identify those that affect the specific software components and versions of those components in your products.
But the sheer volume of vulnerabilities means this should be automated as much as possible to keep it manageable. Another key requirement is to keep false positives — those vulnerabilities that appear to affect your product but really don’t — at a minimum, so you are not wasting time and resources chasing ghosts.
For example, our Vigiles service enables you to load a secure and private product manifest that is then subjected to security vulnerability scanning to pinpoint any vulnerabilities that affect it specifically (Figure 1). The system automates the CVE scanner process so that your team does not spend any time filtering through hundreds of vulnerabilities manually.
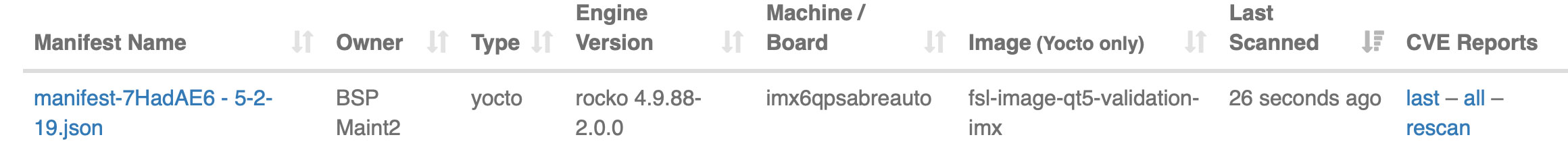
Figure 1: Timesys Vigiles enables easy scanning of a product manifest to pinpoint vulnerabilities that affect your product specifically.
2. Triage & vulnerability assessment
Not all vulnerabilities are equal. Just because a vulnerability is flagged for one of your product components, it doesn’t mean it poses a real risk to a customer in production.
Triage of the vulnerability severity, security risk assessment for it, and evaluation of production deployment modes are all parts of a good assessment process.
For example, CVEs have a severity score that can be a starting point for evaluating the impact and risk posed by the vulnerability.
But a severity 8 CVE may not have an impact on your particular product if the main attack vector used to exploit the CVE is not present in your configuration. For example, if the CVE would require network connectivity for an attacker to exploit it, your product is not at great risk if it is an air-gapped system with no external networking.
Our Vigiles vulnerability management features includes the ability to sort, filter and report on vulnerabilities based on severity. The Vigiles vulnerability list dashboard (Figure 2) also identifies the threat vector for a particular CVE affecting your product, enabling you to quickly assess if a particular vector is relevant to your product configuration and deployment mode.

Figure 2: The Vigiles vulnerability management dashboard permits easy communication and collaboration among team members to triage vulnerabilities and coordinate plans to address them.
3. Mitigation
Once the potential threat assessment is complete for a CVE, the next step is to identify the correct procedure to mitigate risk for customers and to fix the security issue.
But doing so efficiently may require many people across the organization to investigate fixes and develop the mitigation plans. So it is essential to ensure these interactions and planning are efficient and easily managed.
Our Vigiles service includes vulnerability mitigation and collaboration tools that enable a team to communicate clearly about each vulnerability, track the work as it progresses, and ultimately fix vulnerabilities quickly and in the right priority.
Many times the right fix for a vulnerability is a patch for the affected component. Our Vigiles Prime service offers “Suggested Fix” notification for vulnerabilities, identifying when a patch is available to address the particular issue (Figure 3). This boost to patch management can be a major time-saver as it cuts time spent manually hunting down code updates and patches and then assessing whether a particular CVE is addressed by the patch.
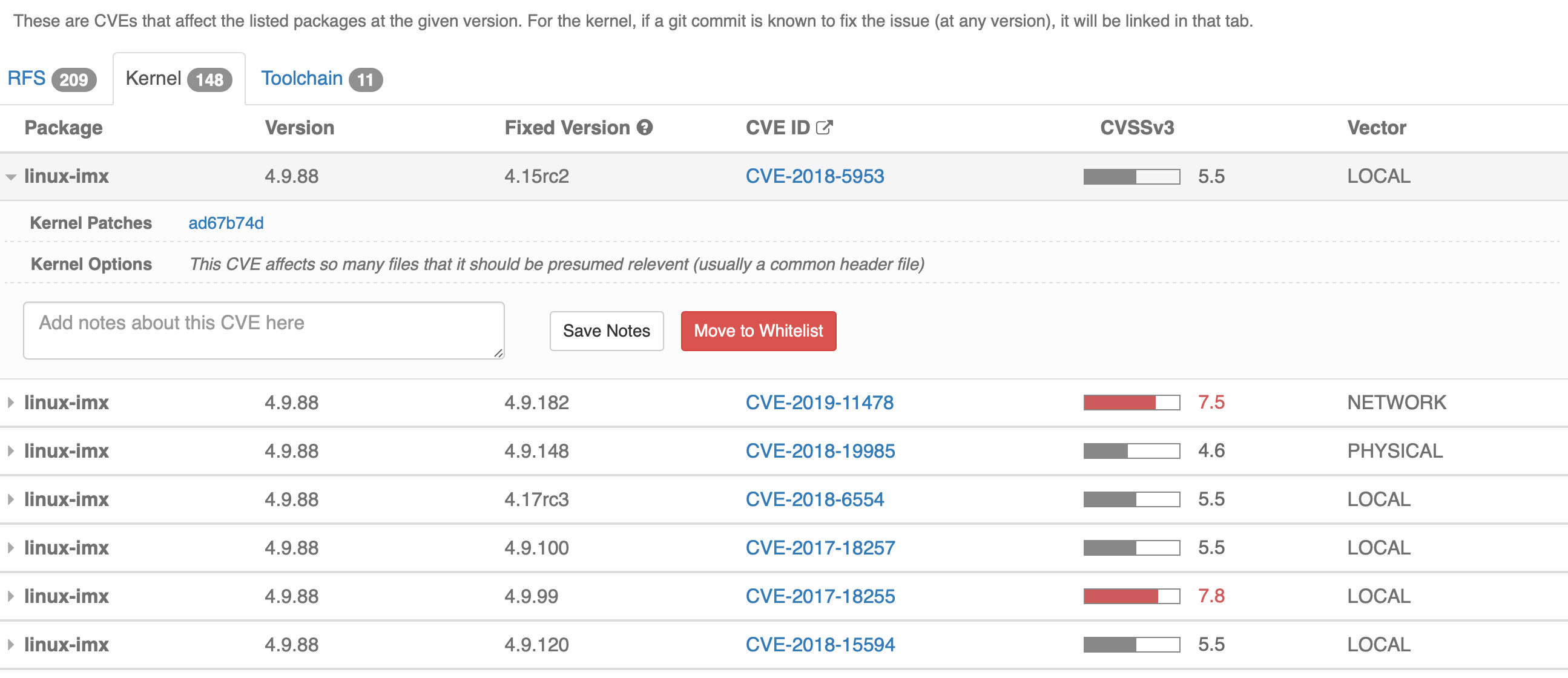
Figure 3: Vigiles Prime provides a link to the Kernel Patch that fixes this vulnerability, streamlining the patch management process.
4. Continuous Monitoring
Your products evolve and the vulnerability environment evolves.
These two moving targets mean you must make vulnerability monitoring and management into a continuous, repeatable process in your organization. As new components are added to your product, or as versions change via updates, it’s important to rescan to identify any old vulnerabilities that have suddenly become relevant.
Vigiles includes a running summary of the fixed and unfixed vulnerabilities in your embedded open source products, providing the bird’s eye view of your progress with improving product security. And with Vigiles you can easily update your manifests as your products evolve.
Organized into an efficient, regular process, the four above steps can significantly reduce the consumption of time and resources needed to maintain a strong security posture in your products. The results are fewer security trade-offs caused by conflicting priorities and constraints.
About Timesys
Timesys has extensive experience with embedded system development and lifecycle management. Timesys has been instrumental in working with global leader semiconductor manufacturers with smart, quick and quality solutions for highly complex systems with accelerated product innovation and multiple product variants.